Connecting To Websites With Self-signed Certificates
Contents
Connecting To Websites With Self-signed Certificates#
What is a certificates?#
As the Web is becoming a more security conscious space, all the major Web browser makers (Google Chrome, MS Edge, Apple’s Safari, and Mozilla’s Firefox) are forcing Web sites to confirm to the more secure way of exchanging information, known as the https protocol. The https protocol requires a lower level communication protocol known as SSL (Secure Socket Layer), which needs a way to exchange trust during the initial connection phase, also known as handshaking.
Trust between the client (e.g. Chrome) and the server (your favourite Website) is established by a method known as key-exchange. Without going into its intricate details, the key-exchange establishes that all future communication between the browser and the server cannot be compromised or stolen by a third-party. The key involved in the handshake is call the certificate.
What is a self-signed certificate?#
In many scenarios, the system may only require secure communication, and not server identity verification. For example, if both the client and the server are restricted behind an enterprise wirewall, then CA signed certificate is not required. Another scenario is if the server is running on a non-standard port. Since many CA only supports https on port 80 and 443, any web server on higher ports must abandon the hope of using a CA signed certificate.
This is when we would use a self-signed certificate during the handshake. The server can generate its own key to ensure secure communication with its clients. But its clients cannot establish server identity.
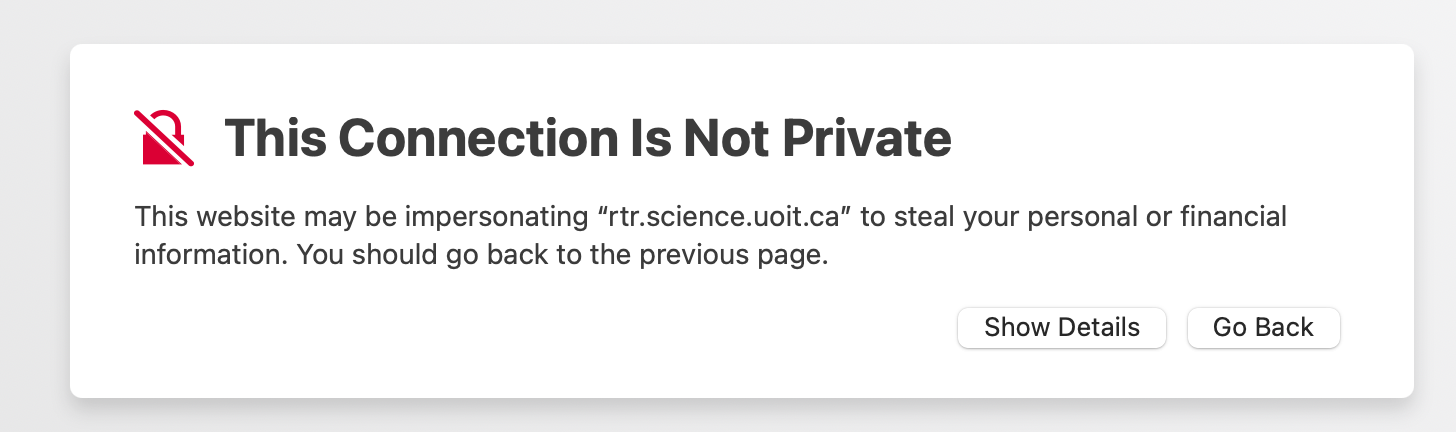
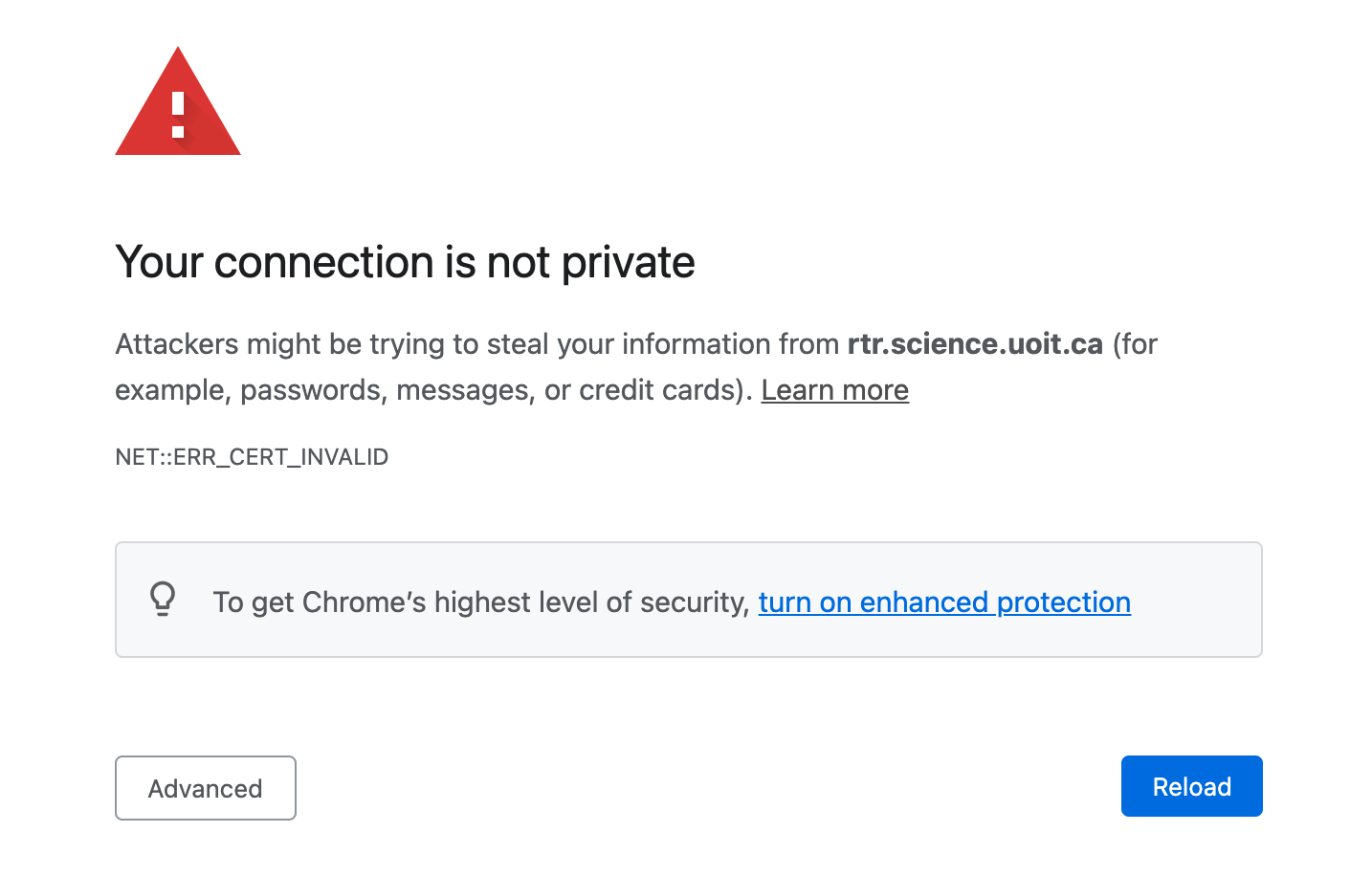
Unfortunately, browsers are not friendly to websites that rely on self-signed certificates.
A warning from Safari.
A warning from Chrome
Coping with self-signed certificates#
If you have confidence in the authenticity of the web server, then you can force Chrome to ignore any cerficate issues.
Google Chrome provides a number command-line flags to modify Chrome’s runtime behaviour. The --ignore-certificate-errors will suppress errors caused by self-signed certificates.
You must launch Chrome from the command line shell, let it be Windows, Linux or Mac OS.
IMPORTANT NOTE
You must ensure that no instances of Chrome are already running. If Chrome is already started, the start-up commands will simply reuse the existing instance of Chrome, which will continue to check for a CA-signed certificate.
So make sure you exist any existing running Chrome instances.
Mac OS#
/Applications/Google\ Chrome.app/Contents/MacOS/Google\ Chrome --ignore-certificate-errors
